Nebraska recently passed the Nebraska Data Privacy Act (Privacy Act).1 The Privacy Act establishes new requirements for businesses to safeguard the personal information of Nebraska residents. The Privacy Act also grants individuals greater rights to access, control, and request the deletion of their data, aiming to enhance transparency of the use of personal data by businesses.
While the Privacy Act is new, the Financial Data Protection and Consumer Notification of Data Security Breach Act of 2006 (as amended in 2018) (in particular, Neb. Rev. Stat. § 87-808, hereinafter referred to as the Security Act) requires Nebraska businesses to institute data security controls commensurate with the sensitivity of the information. The statute in part states:
To protect personal information from unauthorized access, acquisition, destruction, use, modification, or disclosure, an individual or a commercial entity that conducts business in Nebraska and owns, licenses, or maintains computerized data that includes personal information about a resident of Nebraska shall implement and maintain reasonable security procedures and practices that are appropriate to the nature and sensitivity of the personal information owned, licensed, or maintained and the nature and size of, and the resources available to, the business and its operations, including safeguards that protect the personal information when the individual or commercial entity disposes of the personal information.2
Based on the plain language of the statute, the Security Act requires businesses to identify information it collects, categorize the information according to its sensitivity, and take appropriate measures to protect the data. The security measures must be appropriate to the sensitivity of the information, but the law does not require absolute security. The security can be tailored to the nature and size of the organization and limited to the resources available to the organization. Thus, smaller organizations with fewer resources or small nonprofit organizations may not have many resources, and therefore are not required to adopt expensive monitoring tools.
The data must be secured throughout its lifecycle. The Security Act even requires that information must be disposed of in a manner that will protect the information. Accordingly, the disposal of any hardware will require that sensitive information is wiped before disposal.
The failure to maintain security of data at the end of its lifecycle is best exemplified with a recent settlement between the Office of the Comptroller of the Currency (OCC) and Morgan Stanley.3 After Morgan Stanley sold some outdated equipment, a purchaser of some of the equipment notified Morgan Stanley that the information on the equipment had not been wiped and was still accessible. After an investigation by the OCC, Morgan Stanley settled the action for $60 million.
The requirements of the statute, though, have not been tested in court, because the attorney general has not brought an action against a business to enforce the statute.
One final note on the Security Act, the first sentence of the Security Act requires businesses to protect data from “unauthorized access, acquisition, destruction, use, modification, or disclosure.” This language is substantially different from the notification provisions of Neb. Rev. Stat. § 87-802, which require notice to the “unauthorized acquisition of unencrypted computerized data.” This language is notably much narrower than the language of the protection provisions of the data security requirements. Thus, the failure to maintain security provisions will not necessarily result in a notification.
Privacy vs. Security
The Privacy Act aims to protect the privacy of information and is focused on the rights of the individual to control the use and access of personal data.
The Security Act, however, aims to proscribe the security measures necessary to protect such information. The Security Act focuses on specific technical controls, policies, and procedures to maintain security through access controls, configuration of networks and systems, maintenance, monitoring, and media protection.
While the acts are separate, they are really two sides of the same coin. Both are focused on maintaining privacy of the data—one through privacy protections, the other through security requirements.
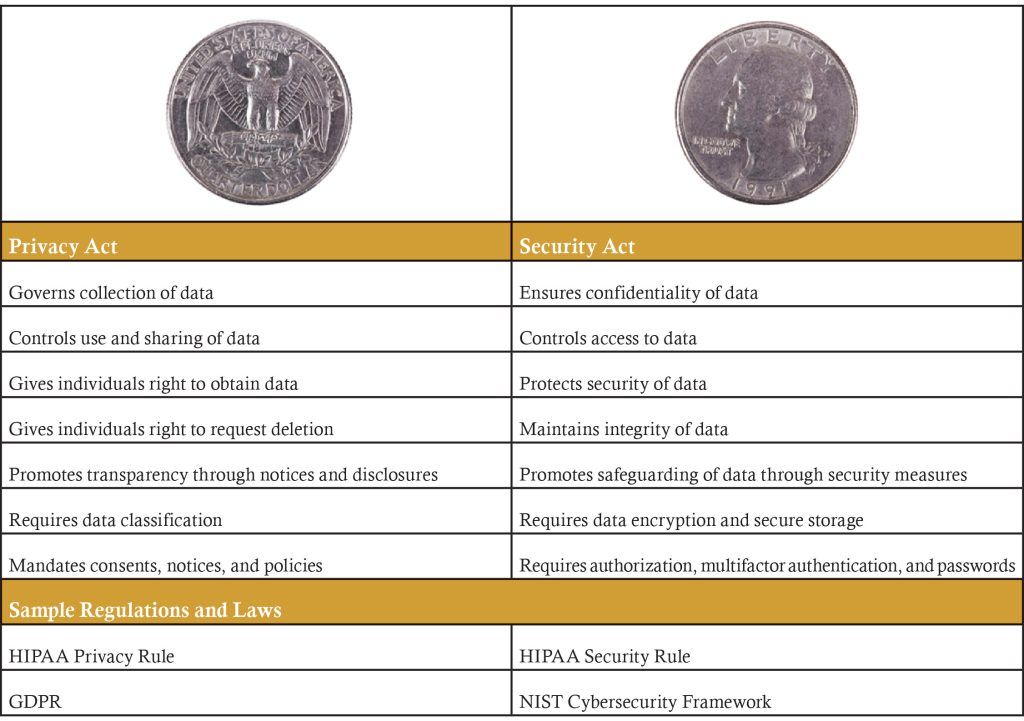
There is also a succinct summary of the differences in Federal Reserve Interagency Guidelines4 as the distinction applies to financial institutions:
Distinction Between the Security Guidelines and the Privacy Rule
The requirements of the Security Guidelines and the interagency regulations regarding financial privacy (Privacy Rule) both relate to the confidentiality of customer information. However, they differ in the following key respects:
-
- The Security Guidelines address safeguarding the confidentiality and security of customer information and ensuring the proper disposal of customer information. They are directed toward preventing or responding to foreseeable threats to, or unauthorized access or use of, that information.
- The Privacy Rule limits a financial institution’s disclosure of nonpublic personal information to unaffiliated third parties, such as by selling the information to unaffiliated third parties. Subject to certain exceptions, the Privacy Rule prohibits disclosure of a consumer’s nonpublic personal information to a nonaffiliated third party unless certain notice requirements are met and the consumer does not elect to prevent, or “opt out of,” the disclosure.
Security Controls & Application of Nebraska Law
As mentioned, the more sensitive the information, the more security controls should be in place to protect that information. For example, information that includes Social Security numbers, financial information, account balances, and information on children, siblings, spouses, etc. should be protected with more security and controls such as multifactor authentication (MFA), virtual private networks, firewalls, auditing and monitoring software, and so forth.
The process of identifying and categorizing information for security protections closely parallels the identification, classification, and data-mapping requirements found in data privacy laws. Both privacy and security require a thorough understanding of all data being collected, saved, used, maintained, and shared or transferred. All data, wherever it may be stored, must be categorized for sensitivity so that proper security controls can be implemented.
At each stage of a file’s digital life cycle, owners of digital data should pause for a complete understanding of the sensitivity of the data to ensure proper controls are identified and implemented. A digital life cycle can include several disparate stages, which may include collection, maintenance, use, archiving, and destruction of data.
Data Collection
When data is initially collected, an assessment should be completed as to the sensitivity of the information and the method used to collect such data. A few simple assessment questions may be appropriate:
- Does the information include any types of data defined as personally identifiable information (PII) under Neb. Rev. Stat. § 87-802, e.g., Social Security numbers, financial account numbers, driver’s license numbers, government identification numbers, or electronic code, routing number, etc.?
- Does the method of collection require encryption in transit and password protection, or is the system protected behind a firewall or virtual private network (VPN)?
- Who is the information being collected from? Does the data provider own the data or provide information on behalf of someone else? Does the data provider have the right to provide the necessary information or consent?
- Is the data being verified when provided?
- Is the data collection process protected with identity verification?
Data Maintenance & Use
- Where is the data being stored, locally or on a cloud-based platform?
- What does the contract or agreement with the storage provider include in terms of cybersecurity procedures, notification procedures, and indemnification provisions?
- Does the platform store the information in an encrypted state? What type of encryption is used, such as cryptographic keys and algorithms used, and who manages the process?
- Who is allowed to access the data, change or modify the data, and delete the data?
- What back-up procedures are in place? Have the backup procedures been tested?
Data Archiving
- When is data moved to an archive, or to the archive state?
- Is the archived data encrypted? And what types of encryption algorithms are used?
- Who has access to the archived data?
- How is the data maintained and/or regularly tested for readability and integrity?
- Is access to the archived data monitored and how long are logs kept?
Data Destruction
- How long is data maintained?
- How is the retention policy enforced?
- Who can authorize the destruction?
- Is the data securely destroyed to ensure it cannot be recovered? Is the data kept on physical devices or in the cloud? How is data wiped from those devices?
- Is a log of data destruction maintained?
- Are procedures in place for reporting and handling the accidental or unauthorized destruction of data?
Conclusion
Applying the Nebraska statutory requirements of the Security Act requires protecting data throughout its lifecycle. Security controls and their application is a multifaceted responsibility that spans people, process, and technology. By asking the right cybersecurity questions at each stage—creation, maintenance, use, archiving, and deletion—organizations can minimize risks and fulfill statutory, regulatory, and compliance obligations. A proactive approach to data security not only mitigates potential threats but also fosters a culture of accountability and resilience in the evolving digital landscape.
Robert L. “Bob” Kardell is an attorney and partner at Baird Holm LLP in Omaha specializing in cyber-breach response, risk management, and fraud investigation. A former FBI special agent with 22 years of service, he is also a CPA, Certified Fraud Examiner, and Certified Information Systems Security Professional. You may reach him at (402) 636-8313 or bkardell@bairdholm.com.
- Nebraska Legislature, LB1074, passed unanimously on April 11, 2024.
- Neb. Rev. Stat. § 87-808, 2018. Accessed Oct. 8, 2025. https://nebraskalegislature.gov/FloorDocs/105/PDF/Slip/LB757.pdf.
- Office of the Comptroller of the Currency, “OCC Assesses $60 Million Civil Money Penalty Against Morgan Stanley,” news release 2020-134, Oct. 8, 2020. Accessed Oct. 8, 2025. https://www.occ.gov/news-issuances/news-releases/2020/nr-occ-2020-134.html.
- Board of Governors of the Federal Reserve System, “Interagency Guidelines Establishing Information Security Standards,” accessed Oct. 8, 2025, https://www.federalreserve.gov/supervisionreg/interagencyguidelines.htm.